Hackers have added a new challenge for corporate HR departments, after targeting companies with a phishing campaign that hides malware in résumés sent as email attachments. The hack, uncovered by Cofense Intelligence a security services provider, uses résumé files attached as .doc to deliver Quasar RAT.
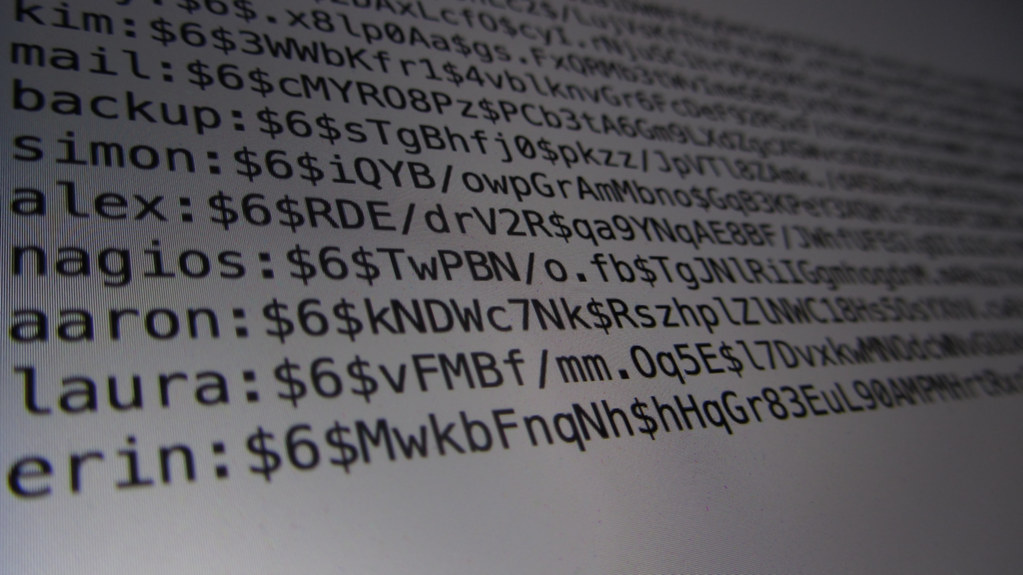
Quasar RAT is a completely legitimate open-source remote administration tool available on GitHub, but it also has a history of being abused. The use of this tool makes it nearly impossible to attribute the campaign to a specific hacking group.
The reports says, organizations have a high degree of difficulty detecting malware within a ‘.doc’ file because the document format can use a multitude of measures to deter detection. For example adding password protection is an option built into Microsoft Word that can make detection of this kind of malicious code nearly undetectable with current tools.
From the report:
“If an analyst or automated system were then to attempt to analyze the macros using an analysis tool (such as the popular tool ‘olevba’ by Philippe Lagadec), the script would fail and potentially crash from using too much memory when it attempted to analyze the macro. This is likely an intentional effect by the threat actor in the form of more than 1200 lines of garbage code that appears to be base64 encoded. Forcing the script to attempt to decode the garbage strings causes, in all likelihood, a crash due to the magnitude of decoding required.”
While the target identified was HR departments and the bait was resumes, the mechanics of this hack could be used with any number of variations. Be Careful about the attachments you open.
Header Image: Christiaan Colen
A small town girl living in a robots world. But these robots only exist online and don’t look like Gabriel Luna. I cover things relating to AI and cybersecurity, topics that are increasingly converging.
Comments are closed, but trackbacks and pingbacks are open.