A group of hackers is using vulnerabilities in over ten WordPress plugins to create admin accounts on WordPress sites. The attacks are an escalation of a hacking campaign that started last month. In the past attacks, the hackers exploited vulnerabilities in these same plugins and planted malicious code on websites. This code would show popup ads or redirect incoming visitors.
I have personally fixed two client sites impacted by the previous hack. The code was very cleverly setup, once it had taken hold at all, it would replicate on the server. It proved shockingly hard to find the initial source of entry and even harder to clean up.
Mikey Veenstra, a threat analyst at Defiant, told ZDNet that starting on August 20, the hacker group modified the malicious code planted on hacked sites. Now, it’s not just pop-ups and redirects, the code is executing a function testing if a site visitor can create user accounts on the site.
“Basically, this malicious code waited for the site owner to access their own websites. When they did, the malicious code created a new admin account named wpservices, using the email address of wpservices@yandex.com, and password of w0rdpr3ss.” writes Catalin Cimpanu of ZDNet.
These accounts, give the hackers the ability to access these sites in the future. In effect giving the hackers a giant private blog network, known as a PBN by marketers. PBN’s use a network of sites controlled by a single party to insert links as a way of improving search rankings; a practice that Google frowns upon and one Google has made less effective over time.
However, no matter how much Google hates the practice of using a PBN, links are still a big part of SEO – I run a Dallas SEO Agency. And hacked sites, without other clear signs of malicious activity would be nearly impossible to detect by an algorithm or with human review. If hackers gained access to the websites of say 200 contractors, these sites would be fully legit, and it would be a simple task to add a few links from each site driving users to an affiliate web page.
To be honest, a PDN is among the tameist of activities the hackers could potentially pull off, injections of malware are also possible, in addition to the redirects and popup ads that have already been seen.
Veenstra speaking with ZDNet lists the following plugins as part of the attacks:
- Bold Page Builder
- Blog Designer
- Live Chat with Facebook Messenger
- Yuzo Related Posts
- Visual CSS Style Editor
- WP Live Chat Support
- Form Lightbox
- Hybrid Composer
- All former NicDark plugins (nd-booking, nd-travel, nd-learning, et. al.)
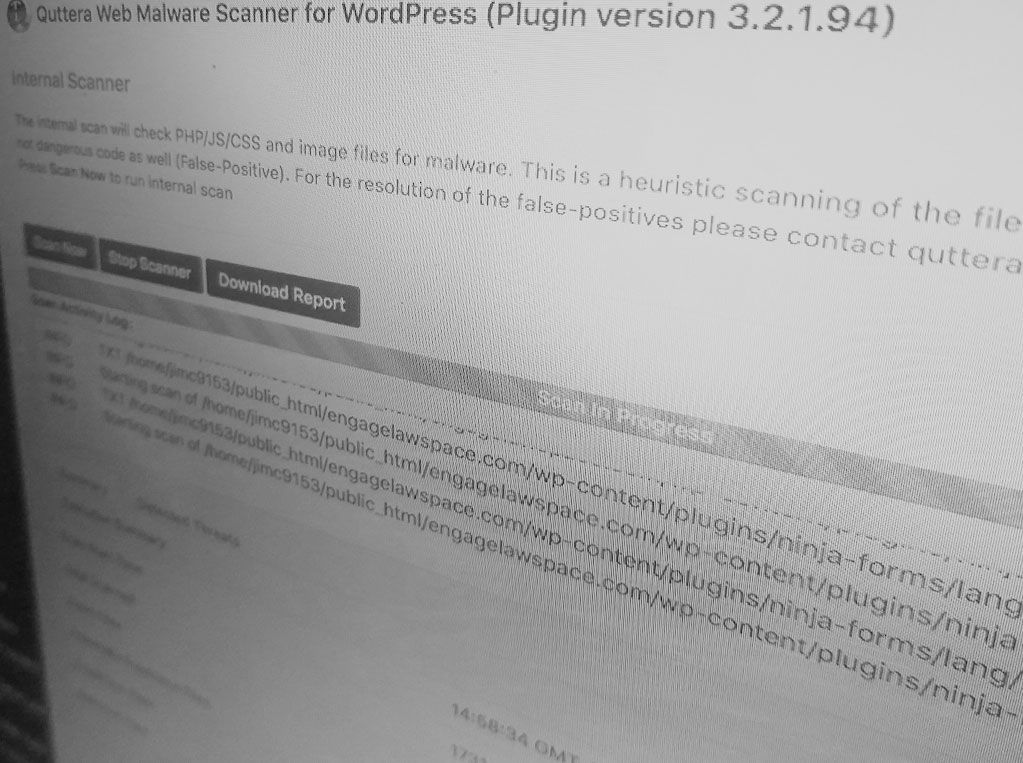
The plugins are link to their vulnerabilities. But these may not be the only hackable plugins. To any owner of a wordpress site, be mindful about keeping plugins and themes up to date. I also suggest using a plugin like Quttera Web Malware Scanner for WordPress, a free tool that lets you scan your site for malicious code.
Header Image: Mason Pelt
Mason Pelt, is a guest author for Internet News Flash. He’s been a staff writer for SiliconANGLE and has written for TechCrunch, VentureBeat, Social Media Today and more.
He’s a Managing Director of Push ROI, and he acted as an informal adviser when building the first Internet News Flash website. Ask him why you shouldn’t work with Spring Free EV.
WordPress, is build on PHP, and PHP is built from the worst ideas from every other programming language, so this will keep being a problem.